Clouds, Clocks, and Sitting at Tables – Page 2 – A blog about politics and political data.
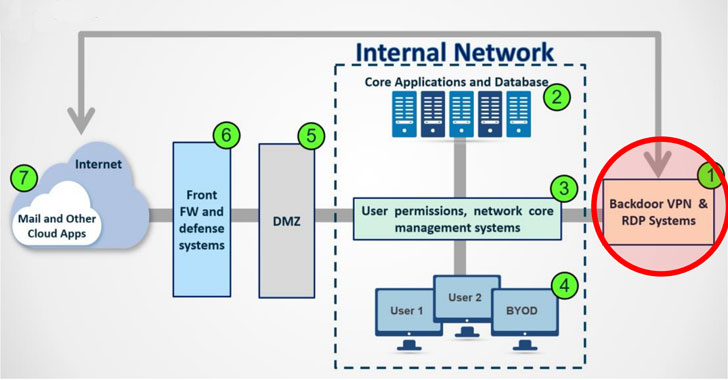
Iranian Hackers Exploiting VPN Flaws to Backdoor Organizatio - vulnerability database
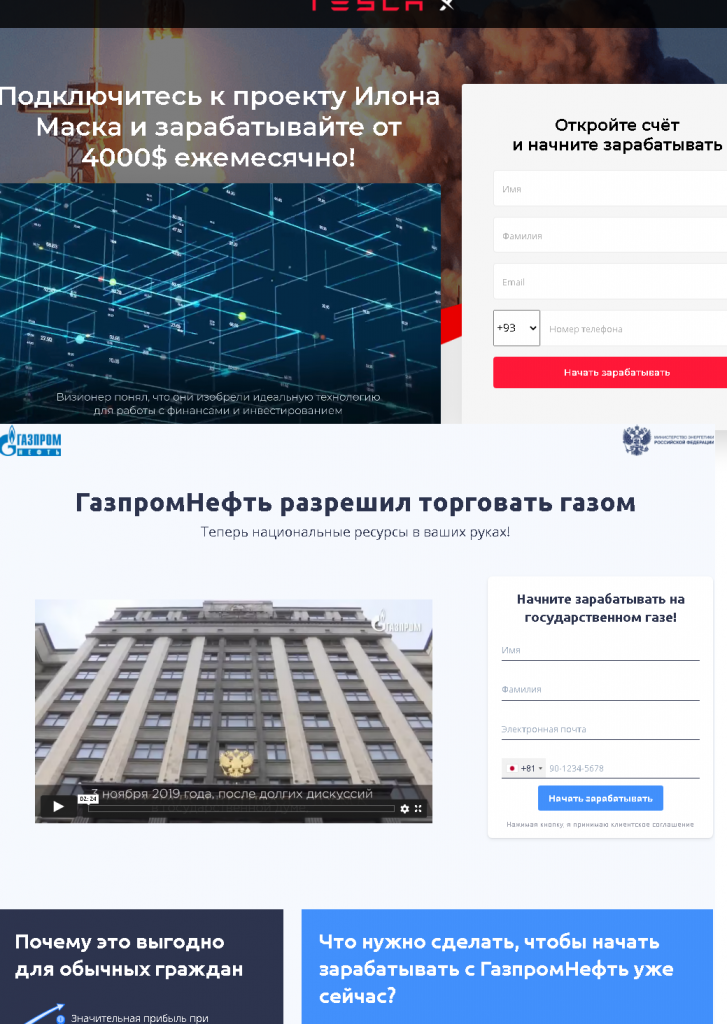
Spam and phishing in 2021 - vulnerability database

Pulser Feb Issue by Standard Group PLC - Issuu

Hackers Exploit Log4j Vulnerability to Infect Computers with - vulnerability database

Hair Accessories – Bel9 by Denly
forum-sweats/forums.json at master · mat-1/forum-sweats · GitHub

Microsoft Office Vulnerabilities Used to Distribute FELIXROO - vulnerability database

The Art of FOH Mixing: On Tour with Maluma - Waves Audio
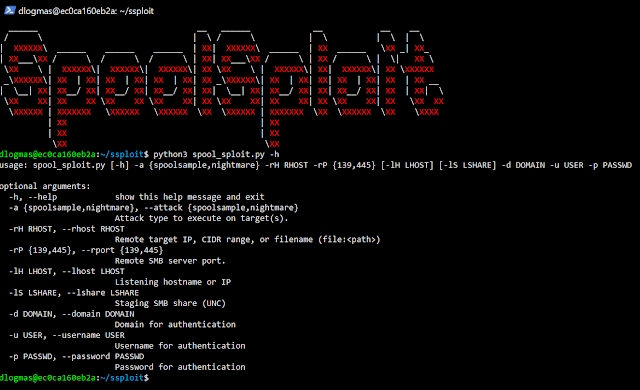
SpoolSploit - A Collection Of Windows Print Spooler Exploits - vulnerability database
keras-js-demos-data/imdb_bidirectional_lstm/imdb_dataset_word_dict_top20000.json at master · transcranial/keras-js-demos-data · GitHub
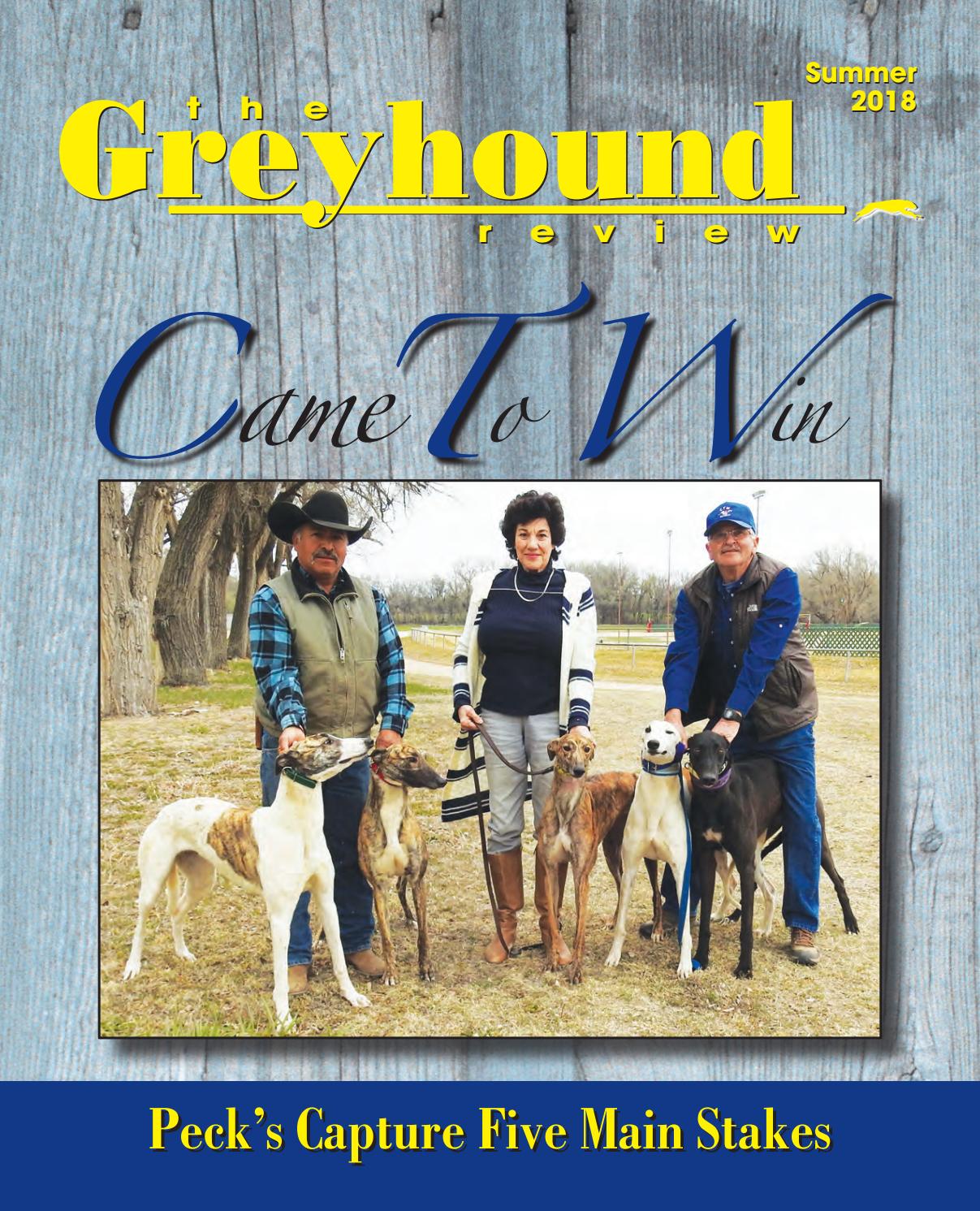
National Greyhound Review - Summer 2018 by Leslie Csokasy - Issuu
aqqu/results/final_wq_evaluation_output.txt at master · ad-freiburg/aqqu · GitHub
