odscon-2015/data/test_with_solutions.csv at master · amueller/odscon-2015 · GitHub
topicModelling/data/text.en.txt at master · balikasg/topicModelling · GitHub

Microsoft Office Vulnerabilities Used to Distribute Zyklon M - vulnerability database

The unknown actual state of artist's work of how artworks how to create wealth in a fake - GIGAZINE

Revolutionizing the Art & Collectibles Industry: Veracity Protocol's Fight Against the Forgery in the Age of AI, by Veracity Protocol

xDedic Market Spilling Over With School Servers, PCs - vulnerability database

The Vast Majority of Antiquities Sold Online Are Probably Looted or Fake, a New Report Says
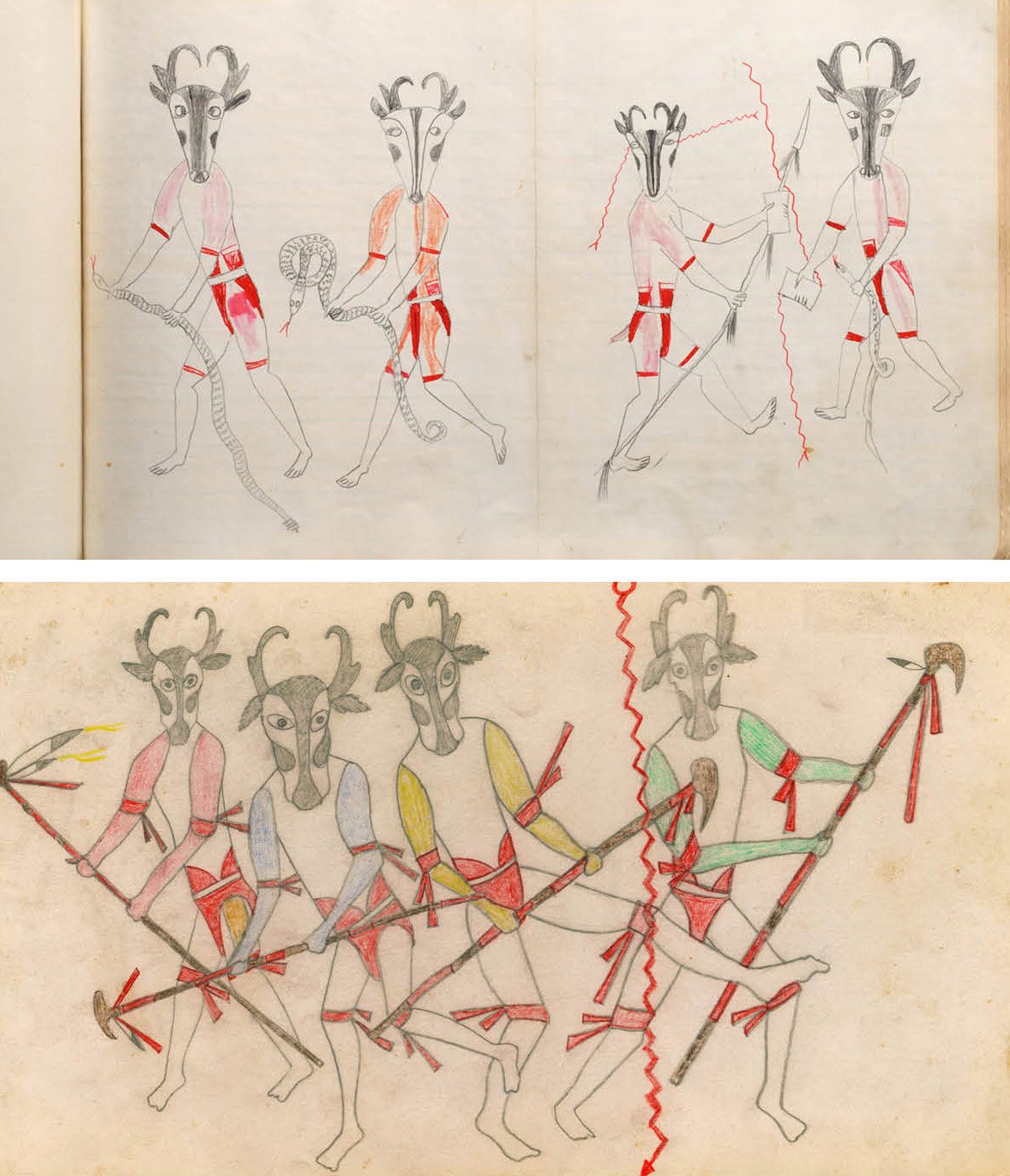
How Possibly Fraudulent and Forged Indigenous Art Ends up in Museums
Grossman LLP, Art Law Blog
HN-Visual-Comments/users.json at master · zmaril/HN-Visual-Comments · GitHub
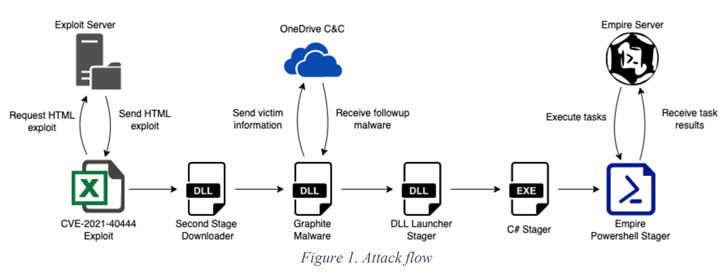
Hackers Exploited MSHTML Flaw to Spy on Government and Defen - vulnerability database

Art forgery ring targeted by FBI raids near Traverse City
hntitlenator/newstories.json at master · victorqribeiro/hntitlenator · GitHub

The Vast Majority of Antiquities Sold Online Are Probably Looted or Fake, a New Report Says
