Blog Archive

Audit Log Review and Management Best Practices

Configuring IBM i Password Security & Composition Rules for Regulatory Compliance - Seasoft

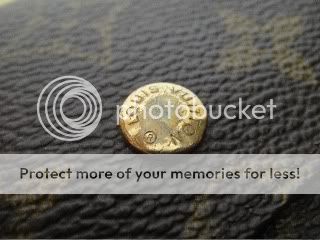
Authenticate this lv: Read the rules & use the format in post #1, Page 104

Deep Dive: How to Automate Every Intake Scenario With a Single Form
Authenticate This LV: READ the rules & use the format in post #1, Page 276

Top 10 IT Issues, 2022: The Higher Education We Deserve

Web Authentication: An API for accessing Public Key Credentials - Level 3

Zero Trust and a New ZT Cryptosystem: Verify, Validate and Authenticate - ATARC